Bitcoin wallets form the interface between the user and the blockchain. They do not store coins, but manage the cryptographic keys that enable access to Bitcoin. The actual Bitcoin is always in the form of UTXOs on the public blockchain, while the wallet only controls the private key that grants the right to issue these UTXOs. Every interaction begins with this key material, which is why the secure storage of the private key is at the heart of every wallet technology. Modern wallets today use a variety of cryptographic standards, protection mechanisms and operating concepts to make handling Bitcoin possible for both beginners and professional users. The rapidly growing variety of wallet types, from mobile hot wallets and hardware devices to off-chain systems such as Lightning or Cashu, reflects the enormous breadth of the Bitcoin ecosystem.
Private keys, public keys and addresses
The foundation of every Bitcoin wallet is the private key, a randomly generated 256-bit value in the form of a long alphanumeric character string. Based on this key, the wallet generates a public key using elliptic curve cryptography, which in turn leads to the generation of the Bitcoin address. In the early years, wallets mainly used addresses in P2PKH format that begin with a "1". With the advent of SegWit, more efficient formats emerged such as P2SH SegWit addresses starting with "3", followed by Bech32 addresses starting with "bc1q" and supporting native SegWit functionality. The most modern form of address is the Taproot address, which begins with "bc1p" and uses state-of-the-art cryptography such as Schnorr signatures, key aggregation and Merkle script trees. This allows complex output conditions to be mapped efficiently and privately, as only a single signature key is usually visible, even if several keys or conditions are hidden behind it.
Seed phrases and the architecture of HD wallets
The BIP32, BIP39 and BIP44 HD wallet standards were developed to simplify the management of multiple keys. The wallet first generates a master seed, which is represented by a 12-, 18- or 24-word mnemonic phrase. This seed phrase is never changed and forms the root material of all subsequently derived keys. Although hundreds of thousands of possible private keys can be generated in the background, the user only needs to keep this one word list secure. Using derivation paths such as "m/84'/0'/0'/0/5", the software recognizes which key belongs to which account and which address. In addition, newer standards such as BIP86 have been developed for Taproot wallets, which will make future multiple signatures more efficient.
Hot wallets
Among the most widespread solutions are mobile hot wallets, which run on smartphones and offer fast, uncomplicated access to Bitcoin. Wallets such as Phoenix from ACINQ specialize heavily in Lightning payments and integrate sophisticated mechanisms such as splicing, in which on-chain BTC and Lightning channels are dynamically merged. Muun works with a hybrid architecture of on-chain keys and automatic submarine swaps, making lightning payments possible without the user having to understand lightning channels or routes. BlueWallet combines straightforward on-chain management with optional Lightning via LNDHub. Breez relies on an embedded non-custodial Lightning node and combines this with extensions such as streaming payments for podcasts. Zeus, on the other hand, is aimed at users who operate their own node and offers extensive remote control for LND, Eclair or Core Lightning. Privacy wallets such as Ashigaru for Android or Wasabi for desktop also expand the range and integrate modern CoinJoin mechanisms. A variety of smaller mobile wallets such as Simple Bitcoin Wallet, Bitcoiner Wallet, Green Wallet from Blockstream or Apex Wallet complete this ecosystem.
Desktop wallets play a particularly important role in the professional sector. Sparrow Wallet is now considered one of the most comprehensive tools for on-chain analysis, PSBT signatures, UTXO management and multi-sig setups. Electrum is one of the oldest Bitcoin wallets and offers a modular, extensible system that supports custom scripts, Lightning integration and hardware wallet connectivity. Specter Desktop optimizes the management of hardware wallets and large multi-sig configurations. Wasabi offers high privacy at desktop level through ZeroLink CoinJoins and automatic anonymization mechanisms.
Mobile hot wallets (on-chain)
- BlueWallet (on-chain)
- Blockstream Green
- Bitcoiner Wallet
- Simple Bitcoin Wallet
- Aqua Wallet
- Apex Wallet
- Ashigaru Wallet
- Wasabi (Mobile Beta)
- Electrum Mobile
Desktop Hot Wallets (On-Chain)
- Sparrow Wallet
- Electrum Desktop
- Wasabi Wallet
- Specter Desktop
- Bitcoin Core (with activated wallet module)
- Fully Noded (Mac)
Note
We do not recommend Wasabi Wallet. Although it presents itself as a privacy wallet, the actual implementation often does not correspond to the expected level of privacy convenience. Many functions appear to be better advertised than they are in practice, which is why other privacy solutions are the more reliable choice in our view.
Cold wallets
Cold wallets are among the most secure methods of self-custody. Classic hardware wallets such as BitBox02, Trezor Model T, Ledger Nano X, Ledger Stax or Blockstream Jade store the private keys on separate chips and sign transactions locally on the device. Even higher security levels are offered by air-gapped devices such as Coldcard, Foundation Passport or DIY solutions such as SeedSigner or Krux. With these devices, keys are generated exclusively offline and transactions are signed via QR codes or SD cards. This means that there is no direct data flow between the device and the internet, which significantly reduces the risk of attacks.
Air-Gapped / High-Security
- Coldcard MK4
- Coldcard Q1
- Foundation Passport
- SeedSigner
- Krux
- Specter DIY
Classic hardware wallets
- BitBox02
- BitBoxNova
- Trezor Model T
- Trezor Safe 3
- Ledger Nano S
- Ledger Nano X
- Ledger Stax
- Blockstream Jade
- Keystone Pro
Note: In the past, Ledger has lost trust in the community due to various decisions and security discussions. If the choice falls on a classic hardware wallet, we therefore recommend devices such as the BitBox02 or the Trezor models, as they are considered to be more transparent and community-friendly.
Paper / Metal Backup (Seed, no device)
- Seedplate
- Cryptosteel
- Billfodl
Multi-sig architectures
Multi-sig wallets distribute responsibility across multiple keys. Typical configurations are two-out-of-three or three-out-of-five key systems where multiple independent devices work together. This means that neither a single device loss nor physical theft of a key can compromise the coins. Tools such as Nunchuk, Sparrow, Specter or Caravan make it easy to set up such multi-sig systems. Modern variants use Taproot-based MuSig2 signatures, which appear to the outside world like a normal single signature, thus saving fees and improving privacy.
Multi-sig capable mobile wallets
- Nunchuk Mobile
- BlueWallet (multi-sig possible)
Multi-sig desktop solutions
- Specter Desktop
- Sparrow Wallet
- Caravan (Unchained Capital)
- Electrum (advanced scripts)
Hardware multisig compatible devices
- Coldcard
- Passport
- BitBox02
- Ledger (with restrictions)
- Trezor
Full nodes and wallets
If you want to manage your Bitcoin with complete sovereignty, you can operate your own full node. Wallets can connect directly to this node, which verifies all transactions itself. This eliminates the need to trust external servers. Systems such as Bitcoin Core, Electrum Personal Server, BTCPay Server or complete node operating systems such as Umbrel, Raspiblitz, Start9 or MyNode enable private or professional node operation.
Wallets that fully verify their data themselves
- Bitcoin Core
- Electrum + own Electrum Personal Server
- Sparrow + own node
- Specter Desktop + own node
- BTCPay Server Wallet
- Umbrel Full Node Wallet
- MyNode Wallet
- Raspiblitz Node Wallet
- Start9 Embasssy Node Wallet
Lightning Wallets
The Lightning Network forms a second layer on top of Bitcoin, enabling almost instant and very cheap transactions. Payments are not written directly to the blockchain, but are processed via payment channels between nodes. Custodial lightning wallets such as Wallet of Satoshi or Blink take over the technical complexity completely and allow easy use, but require trust in the operator. Non-custodial wallets such as Phoenix, Breez or Zeus enable Lightning self-custody and use modern technologies such as multi-path payments and splicing to make operations as transparent as possible for the user.
Custodial Lightning wallets
- Wallet of Satoshi
- Blink Wallet
- Strike (partially custodial)
- Coinos
- Alby Browser Wallet
Non-Custodial Lightning Wallets
- Phoenix
- Breez
- Zeus
- Muun (technically hybrid, but non-custodial for on-chain keys)
- Electrum Lightning
- Eclair Mobile (older, but exists)
- Blixt Wallet (Lightning + LNURL)
Lightning node wallets (with their own node)
- Zeus (with LND / CLN / Eclair)
- Thunderhub
- RTL (Ride The Lightning)
- LNbits wallets
- Umbrel Lightning Wallet
Cashu - Bitcoin-Ecash
Cashu is a new off-chain technology that is completely designed for privacy. The functionality is based on Chaumian Blind Signatures, where the mint signs tokens without being able to recognize who they belong to. This creates a system that enables lightning-fast, private and virtually fee-free transactions. Wallets such as Nutshell, Cashu.me, eNuts or Minibits implement this principle. Although Cashu is technically custodial, it enables a level of privacy that both on-chain and Lightning hardly achieve.
Cashu wallets (Chaumian Ecash)
- Nutshell Wallet
- Cashu.me Wallet
- eNuts Wallet
- Minibits Wallet
- NUTS CLI Wallet (command line)
- Strobe Wallet
- Phoenix-Cashu (experimental)
Advantages and disadvantages
Bitcoin wallets each offer different strengths and weaknesses. Hot wallets are easy to use, but are naturally online and therefore more susceptible to attacks. Cold wallets offer maximum security, but require more care when setting up. Multi-sig increases security, but requires structure and documentation. Lightning wallets are ideal for everyday, fast payments, but are technically more complex. Finally, Cashu offers great speed and privacy, but requires trust in the respective Mint.
Protecting privacy with Bitcoin
Privacy wallets aim to increase the financial privacy of users by making data leaks, on-chain analysis and movement profiles more difficult or impossible. While Bitcoin as a system is transparent, suitable wallet software nevertheless creates very strong privacy layers, whether through Coin Control, CoinJoins, PayJoin, Tor integration or the use of alternative cryptographic systems such as Monero transactions. Two wallet projects that are receiving more and more attention in this area are Cake Wallet and Ashigaru.
Bitcoin privacy wallets
- Ashigaru Wallet (a fork from Samourai Wallet)
- Fully Noded
- Simple Bitcoin Wallet (with extended UTXO options)
- Zeus Wallet (private, if via own node)
- Electrum (private only via own node + Tor)
- Specter Desktop (full node privacy)
- StackDuo, Stack Wallet (private only via own node + Tor)
Multi-asset wallets with strong privacy features
- Cake Wallet (Bitcoin via Tor)
- Aqua Wallet
- BlueWallet (on-chain private, if via own Electrum server)
- Exodus (limited, but with Tor option on desktop)
Node-based private wallets
- Bitcoin Core Wallet (completely private via own node)
- Sparrow Wallet + own node
- Electrum + Electrum Personal Server
- Specter Desktop + own Bitcoin Core
- Fully Noded (iOS) + own node
Tip
The Cake Wallet is suitable for both Monero and Bitcoin and is characterized by a strong focus on privacy. The team is considered to be very progressive and has consistently delivered high-quality work in the past.
The Ashigaru Wallet is a modern and recommendable alternative to the Samourai wallet and offers strong privacy features without unnecessary complexity.
If you need maximum control over your Bitcoin, the Sparrow Wallet is an outstanding solution. It is considered one of the best options for users who prefer complete transparency, precise UTXO management and in-depth control.
Note
For strong privacy, Wallet and Node should always be configured via Tor at all times. If you are serious about data protection, you should also run a own nodeso that no external servers can see your data. Particularly privacy-focused Bitcoiners also rely on open source operating systems for their nodes - so don't use Umbrel, but rather an x86 node, StartOS or the Ashigaru Node.
Best practices for self-custody
If you want to self-custody Bitcoin, you should follow some basic security principles. One of the most important measures is to operate the wallet and node consistently via Tor so that no connection can be traced directly to your IP. In addition, having your own Bitcoin node significantly increases your privacy and security because you are not querying transactions and addresses via third-party servers. Many privacy-oriented Bitcoiners also rely on open source systems in order to retain control over their infrastructure. The correct handling of the seed is just as important: never take screenshots, never save them digitally and always back them up offline, preferably on robust metal backup disks. These few basic rules form the basis of secure and sovereign Bitcoin custody.
Partially Signed Bitcoin Transactions
PSBTs play a central role in the use of cold wallets or multi-sig setups. A PSBT is a partially signed Bitcoin transaction that is exchanged between devices without the private key ever leaving the secure hardware wallet. The software wallet (e.g. Sparrow or Specter) builds the transaction, saves it as a PSBT and transfers it to the hardware device, e.g. via SD card or QR code. There, the transaction is securely signed and then returned to the software, which broadcasts it to the network. PSBTs therefore make it possible to use cold storage systems and hardware wallets securely, even in complex multi-sig configurations.
UTXO management
Bitcoin is based on the principle of so-called UTXOs ("Unspent Transaction Outputs"). Each incoming payment generates a new, independent UTXO, which is treated like a single "banknote" in your wallet. A wallet therefore does not consist of a single account balance, but of many individual UTXOs of different sizes.
UTXO management means keeping track of how many UTXOs you have, how big they are and which transactions they originate from. Well-structured UTXO management helps to keep fees low, better understand your own history and ensure a clean allocation of holdings in the long term.
If UTXOs grow in a disorganized manner, unnecessarily high fees can arise later on, as a large number of small UTXOs can lead to an expensive, large transaction. Similarly, disorganized UTXO structures can compromise privacy, as different payment histories could be unintentionally linked.
Conscious UTXO management therefore ensures that the wallet remains efficient, traceable and cleanly structured - and forms the basis for later steps such as privacy tools, multi-sig setups or long-term cold storage strategies.
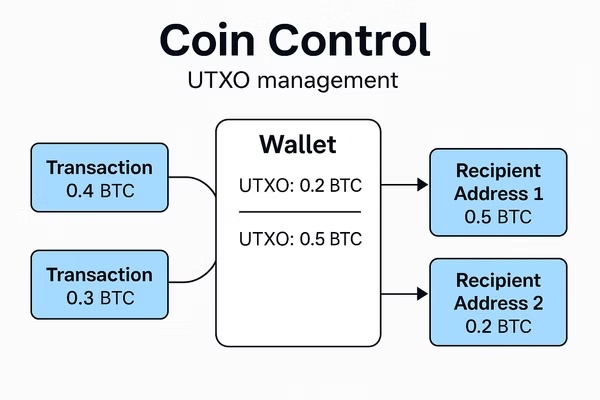
Coin Control
Coin control (or UTXO management) means that you choose which of your UTXOs are used for a transaction. A UTXO is an "incoming coin", i.e. the amount you have received from a previous transaction. Your wallet can consist of many small and large UTXOs, similar to different banknotes in a wallet.
The graphic shows this principle
For example, the wallet has two UTXOs, one for 0.2 BTC and one for 0.5 BTC. When you make a payment, you can decide which one should be used. This prevents UTXOs from different sources from being mixed and unintentionally revealing information about your history. At the same time, Coin Control helps to avoid unnecessarily high fees by specifically selecting smaller or larger UTXOs.
Without Coin Control, your wallet can automatically mix UTXOs that should actually remain separate. This can dilute CoinJoin results and blockchain analytics can better recognize correlations. With Coin Control, you retain full control over privacy, fees and the structure of your wallet.
Conclusion
Bitcoin wallets are much more than simple apps or devices - they are the key to true financial self-determination. The wide variety of wallet types shows that users can use completely different tools depending on their needs: From mobile hot wallets for everyday use, to hardware wallets for long-term security, to lightning and cashu systems for fast and private off-chain payments.
If you want to manage Bitcoin confidently, you need to develop a basic understanding of the technical concepts: UTXOs, coin control, PSBT workflows, node connectivity and the importance of the seed phrase form the basis for secure self-custody. Privacy-oriented users in particular benefit from tools such as Sparrow or Ashigaru, which offer deep control and strong data protection mechanisms.
In the end, everyone decides for themselves how much responsibility they want to take on. But the more you understand and the more you master the tools, the stronger your independence becomes. Bitcoin rewards precisely this combination of knowledge, discipline and the willingness to protect your own assets. If you use your wallet confidently, operate Tor and your own node and store seeds securely offline, you not only hold your Bitcoin in your own hands, but also your privacy.
---
Disclaimer
The information contained in this article regarding Bitcoin wallets, seed phrases, backup methods and security procedures is for educational purposes only and does not constitute legal, tax or financial advice. For individual decisions, you should seek expert advice if necessary.
We assume no responsibility for the accuracy, completeness or timeliness of the content. Liability claims for damages arising directly or indirectly from the use of the information described - for example due to theft, operating errors, technical problems or loss of access data - are excluded to the extent permitted by law.
The mention of specific products or procedures does not constitute a recommendation. Always check the security features and legal framework independently. Regulations on cryptocurrencies may vary and change depending on the country.
The safekeeping of Bitcoin - in particular the handling of seed phrases and backups - is at your own risk. Take appropriate security precautions according to your personal protection needs.




