
In recent years, the debate surrounding quantum computers has reached a level that is both scientifically and socially remarkable. New reports about progress at Google, IBM or other research institutions appear almost weekly, while the media and voices from the technology world warn that such a technological breakthrough could shake the foundations of modern cryptography. Here, more than with almost any other topic, sober science, irrational fear, economic interests and technological ignorance collide. At the heart of it all is Bitcoin - the world's first fully decentralized digital money system based on mathematical security. This makes it all the more important to take a comprehensive view that not only conveys technical facts, but also takes into account the structural, political and historical characteristics of Bitcoin.
Why quantum computers could affect Bitcoin at all
A classic computer works sequentially and deterministically. It processes data in bits that assume either the state 0 or 1. The entire digital world is based on this binary architecture. A quantum computer is fundamentally different because its basic unit, the qubit, can assume several states simultaneously thanks to quantum physical phenomena such as superposition and entanglement. These properties enable quantum computers to solve very specific mathematical problems that classical computers could either not solve at all or only with astronomical amounts of time.
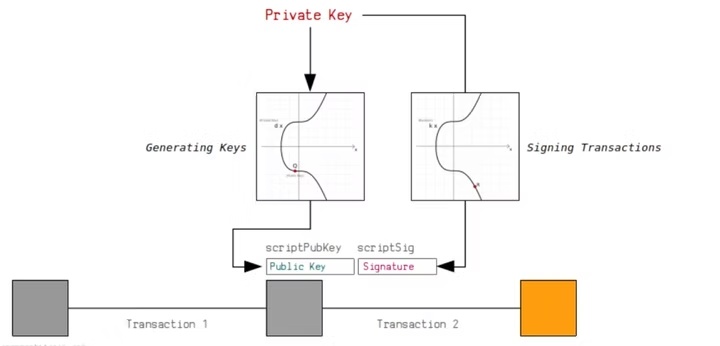
The cryptography that protects Bitcoin is based on precisely such mathematical problems - especially those that are easy in one direction and practically unsolvable in the other. In essence, this means: It is easy to generate a public key from a private key, but extremely difficult to recalculate the private key from a public key. For classical computers, this back-calculation is practically impossible. For a future quantum computer, however, Shor's algorithm could theoretically accomplish this task, and this is where the technical relevance begins.
The real danger therefore does not arise from the fact that a quantum computer could "hack everything", but from the possibility of inverting mathematical problems on which Bitcoin signatures are based. Even the theoretical possibility is enough to pose a serious, long-term threat. But there is a long way between theory and practice - and this must be considered carefully and without panic.
How far quantum computers really are
Although research has made enormous progress, the idea of a ready-to-use quantum attack system is greatly exaggerated. Today's most powerful quantum computers only have a few hundred to a few thousand physical qubits. However, it is not the physical qubits that are decisive, but the logical qubits, which must be stabilized by error correction. Each logical qubit requires a large number of error-prone physical qubits.
To realistically threaten the elliptic curve cryptography that Bitcoin uses, hundreds of thousands to millions of logical qubits would be required. This exceeds today's technological capacity by orders of magnitude. Estimates by serious experts speak of possible breakthroughs in the period between 2030 and 2040, although these are mere approximations. Perhaps it will happen sooner, perhaps later. The future of quantum technology research is fundamentally unpredictable.
In addition, many advances reported in the media are based on theoretical laboratory results or very specific test conditions. A quantum computer that can perform a computation under idealized laboratory conditions is completely different from a robust, scalable, error-corrected system capable of computing real-world, complex cryptographic parameters. The difference between "feasible in the lab" and "operational in reality" is enormous.
How a Google roadmap became a Bitcoin alert
A large part of the current quantum panic surrounding Bitcoin can be traced back to a single misunderstanding. Google published a scientific research paper on the development of certain quantum protocols. No year was mentioned in the paper to indicate a specific threat. However, in a supplementary blog post, Google stated that it wanted to make its own infrastructure completely "post-quantum ready" by 2029.
This internal objective was wrongly interpreted by the media as a prediction that Bitcoin would become insecure from 2029. This conclusion is not drawn in any scientific publication. Rather, it stems from journalistic misinterpretation and a general sensationalism that confuses technical roadmaps with threat scenarios. The idea that Bitcoin will be cryptographically vulnerable in a few years is not tenable based on the current state of research.
Visible public keys and old addresses
While modern Bitcoin addresses are protected by the hash function, there is an earlier generation of addresses that were used in the early years of the network: the so-called pay-to-public key addresses. They reveal the public key directly and permanently. It is estimated that some of these addresses belong to Satoshi Nakamoto himself and may contain around one million Bitcoin.
If a quantum computer ever becomes powerful enough, calculating the private key from a publicly visible key would be the first realistic attack surface. The economic attractiveness of an attack would be unprecedented. Even the movement of these early coins would cause panic - whether through an attack or Satoshi's own decision to move them. The combination of technical vulnerability and symbolic significance makes these addresses a special category of risk that cannot be ignored.
Visible public keys and old addresses
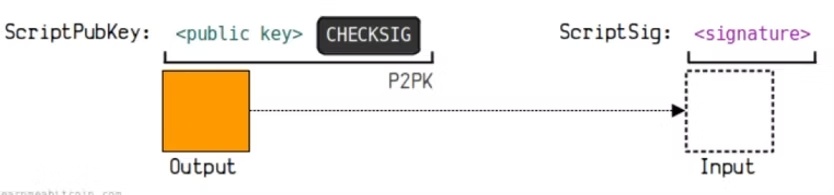
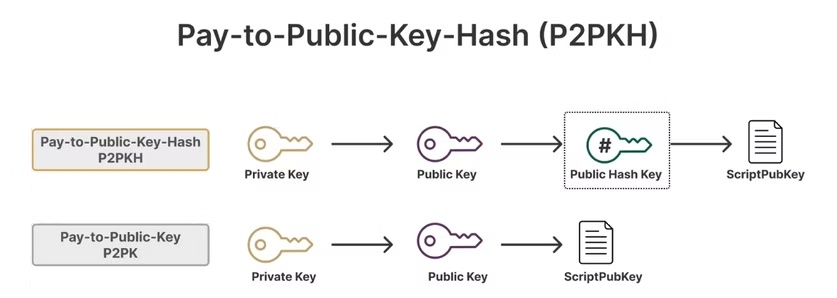
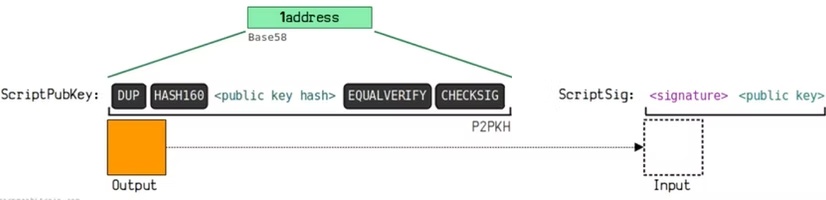
Not every Bitcoin address is equally at risk. An important difference is often overlooked: The earliest addresses in the Bitcoin network are so-called pay-to-public-key addresses (P2PK). With these addresses, the complete public key is permanently and openly stored in the blockchain.
In asymmetric cryptography, a public key is the part that you can share with others; it is not enough on its own to move funds - the private key is required for this. However, certain attack methods (based on an Sh algorithm, for example) could derive the private key from a public key, which is why P2PK addresses are a direct target.
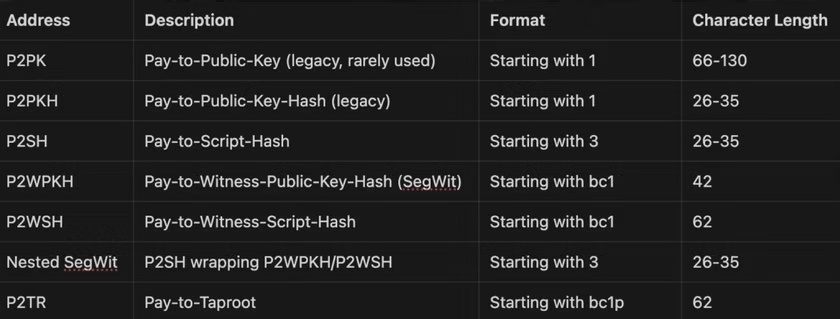
Protection through hash-based address types and 10-minute windows
Newer address types, on the other hand, initially only show the hash of the public key. A hash is a one-way function: a fixed output value can easily be calculated from the input, but the original input cannot be reconstructed from this value. As long as you have never sent from such an address, your public key remains hidden - and without a visible public key, an attack using key derivation is not possible. Only when you sign and send a transaction does the public key appear in the network; there is a short but critical time window until confirmation in the next block - about 10 minutes.
Current research results (including from Google) indicate that a powerful quantum computer could theoretically carry out an attack within this time window. This is a future risk, but not the only problem.
Satoshi problem
The bigger risk is what I call the "Satoshi problem". Satoshi Nakamoto, the anonymous inventor of Bitcoin, used P2PK addresses in the early years and apparently collected large amounts of Bitcoin - estimates say around one million BTC, today a double-digit billion amount. These coins have not been moved for years; the associated public keys have been visible in the blockchain ever since. Should a cryptographically relevant quantum computer exist at some point, these addresses would be vulnerable to attack for the first time - not because the technology is simpler per se, but because the potential gain would be enormous. A successful attack on these stocks would probably trigger panic, a massive loss of trust and a dramatic fall in prices. Even if Satoshi were still alive and had access to the private keys: as soon as these coins were moved, the situation would inevitably escalate.

Altcoins
ECDSA as a signature process is shared by almost all major cryptos. Ethereum is just as affected as Bitcoin. The key difference lies in governance. Ethereum has an active core development team that explicitly has post-quantum migration on its radar and can communicate with the Ethereum ecosystem. That doesn't necessarily mean it's easier, but the governance structure makes it a little easier here. The situation is similar for many other coins. Some coins are already post-quantum secure and others are actively being implemented.
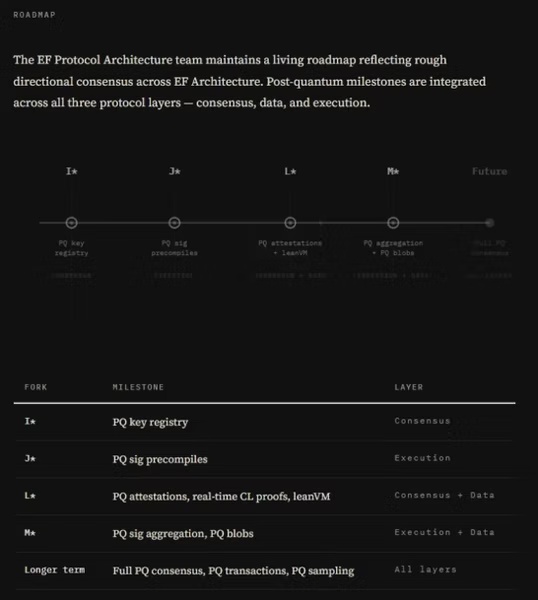
Why the biggest vulnerability is not cryptography, but Bitcoin governance
Although the technical problems appear difficult, they are in principle solvable. The cryptography community has long since developed post-quantum algorithms that are secure against Shor's algorithm. NIST ratified corresponding standards in 2024. The hurdle therefore lies less in the software than in the structure of the Bitcoin network.
Bitcoin is completely decentralized. There is no central institution that can authorize or enforce a protocol change. Any major change requires global cooperation across national borders, languages, cultures and interest groups. The blocksize debate in 2017 has already shown how difficult it is to find consensus. A post-quantum migration would be far more complex, as it concerns not only efficiency, but the fundamental question of ownership. Wallets that have not been moved for years - whether through forgetting, loss or death - could become targets of attack if their owners do not migrate in time.
This issue touches on the fundamental principle of Bitcoin: no one can be forced to change their behavior. From a decentralized perspective, this is a feature. In the context of a necessary migration, however, it is a serious structural risk.
A challenge that does not overwhelm Bitcoin, but is demanding
Bitcoin has proven in the past that it is technologically adaptable - albeit slowly, carefully and as part of a global, anarchic consensus process. The threat of quantum computing is forcing the network to take a long-term view. The good news is that there is time. The bad news is that time alone is not enough if coordination does not work.
Science provides the solutions. But whether these solutions are implemented in time does not depend on engineers, but on whether a global community without leadership, without central authority, without binding communication channels and without coercion can achieve the necessary unity.
Who would even allow a quantum computer to be attacked?
Even if a really powerful quantum computer were to exist tomorrow, the crucial question is who would actually use it for an attack. Large technology companies such as Google, IBM and Microsoft are developing quantum computers for completely different purposes - such as medical research, materials science, climate modelling or complex optimization problems. For these companies, an attack on financial systems or global encryption would not only be pointless, but also extremely risky and legally disastrous.
In the long term, however, access to this technology will not remain with Western research institutions. Countries with completely different interests and fewer legal barriers could also have such systems at some point. This means that even if nobody attacks Bitcoin today, this situation could change in the future. The mere existence of a sufficiently powerful quantum computer could create uncertainty because markets always price in risks. Even without a single real attack, the mere announcement of such a breakthrough would trigger crises of confidence.
Quantum computers are not currently an immediate threat. Development is progressing, but the technological gap is still large. At the same time, the world has long been working on solutions. The first binding post-quantum standards were published in 2024, and a large part of the digital infrastructure is already in the process of being converted.
Why state actors would be the real danger
A crucial point in the discussion about quantum computers is who would actually use this technology later on. While large technology companies have no interest in attacking encryption, this does not necessarily apply to all states. Some countries - such as North Korea - have already shown in the past that they finance their political and economic goals through cyber attacks. If such a state were to gain access to a truly powerful quantum computer at some point, the threat situation would change fundamentally, as the threshold for attacks there is significantly lower than for Western companies or democracies.
There is also a second, psychological danger: even if an actual attack never takes place, the mere possibility of a quantum attack could shake confidence in existing systems. Financial markets are sensitive to risks - and even the news that a cryptographically relevant quantum computer exists could trigger uncertainty and crises of confidence long before anything happens.
Could quantum computers speed up Bitcoin mining?
The concern that a future quantum computer could suddenly have enormous advantages in Bitcoin mining is technically unfounded. Bitcoin mining relies entirely on SHA-256 hashing, and it is precisely this type of calculation that is not suitable for quantum computers. While Shor's algorithm can only attack signatures, Grover's algorithm only provides a theoretical quadratic speedup for hash functions - far too low to outperform specialized ASIC miners. Bitcoin mining requires billions of hash attempts per second, a performance that current and foreseeable quantum computers can neither perform stably nor fast enough. In addition, a miner would have to constantly try out new templates and nonces, which quantum computers are technically unable to do efficiently. This is why ASICs will remain the undisputed technology in mining in the long term, while quantum computers offer no practical advantage here.
Bitcoin and the test of the century
Bitcoin was created to exist independently of states, companies and individuals. It is a network that can only be changed by consensus. It is precisely this characteristic that makes it resilient - and at the same time vulnerable to challenges that require collective action. The real question is not whether quantum computers will one day be strong enough to break today's cryptography. The real question is whether Bitcoin, as a global, decentralized system, will be able to prepare for the post-quantum era in a timely and unified manner.
There is no reason to panic, but there is also no reason to be careless. The future of quantum technology is uncertain, but the direction is clear: Bitcoin faces a long-term but solvable challenge. How the network responds will determine whether Bitcoin remains what it is today in the age of quantum computing - the most robust, independent and censorship-resistant monetary system in the world.
---
Important note
The opinions and information provided by us do not constitute financial advice. They are for informational and educational purposes only and are not intended as a substitute for individual advice from qualified professionals.
---






